Detecting Initial Access: HTML Smuggling and ISO Images — Part 2
In the previous blog in this series, we extracted behavioral TTPs, prepared the attack emulation, and executed it.
It’s time for analyzing the logs, validating/modifying the hypotheses that we generated after reading the report(or generating new ones), generating detection strategies, and developing detections.
Analyzing the Logs
I analyzed the Microsoft Defender for Endpoint logs, but you can check Sysmon or your EDR logs. Although there can be other events generated during the attack, below are the most important ones for me to generate or validate hypotheses:
1. Mounting an ISO image generates the below Registry event:

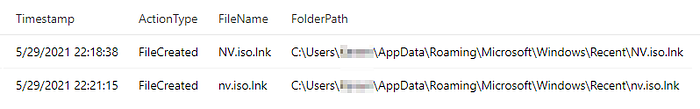
2. Opening the mounted image generates a file creation event:
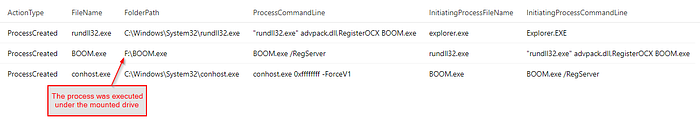
3. Double-clicking the shortcut file generates the below process execution events:
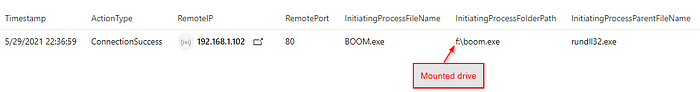
4. Execution of the payload(BOOM.exe) generates a network connection event:
Validating/Modifying the Hypotheses
I already generated some hypotheses after reading the report. Alternatively, you can generate your hypotheses after the emulation and analysis of the logs.
I intentionally skipped some hypotheses as they were fragile. For example:
- Outlook creating an HTML file (can be bypassed with a .zip)
- rundll32 execution (can be replaced by another technique)
To me, generating as few hypotheses as possible with enough coverage to detect the attack is important(less is more + Pareto). If I can cover almost all possibilities with a few hypotheses, it will make my life easy.
Going back to the attack, since we have the folder name, we can use it for finalizing our hypotheses.
Final hypotheses
- ISO file creation is highly suspicious on non-IT users’ computers
- Process execution under a mounted drive can be highly suspicious
- Network connection from a process that runs under a mounted drive can be highly suspicious
We need to check if these hypotheses generate hide fidelity results. To check the 2. and 3. hypotheses, we need to correlate the Registry event with process creation and network connection events. This is possible if you can query logs and generate new fields.
After analyzing the logs historically, I saw all three hypotheses were valid and would generate high fidelity results.
Creating Detections
I’ve created 3 queries for Microsoft Defender for Endpoint, 3 queries for Azure Sentinel (Sysmon) and published them in my GitHub repo. You can use the same logic on your own tool.
Conclusion
In this post, I used a different approach for TTP extraction without fully using the MITRE ATT&CK framework and wanted to show alternative ways of detecting attacks. I also wanted to show detecting Initial Access is still possible. I hope you stop assuming the breach and start hunting/detecting initial access as an additional effort in your threat management program.
I’ll keep posting blogs about initial access detection. Stay tuned…